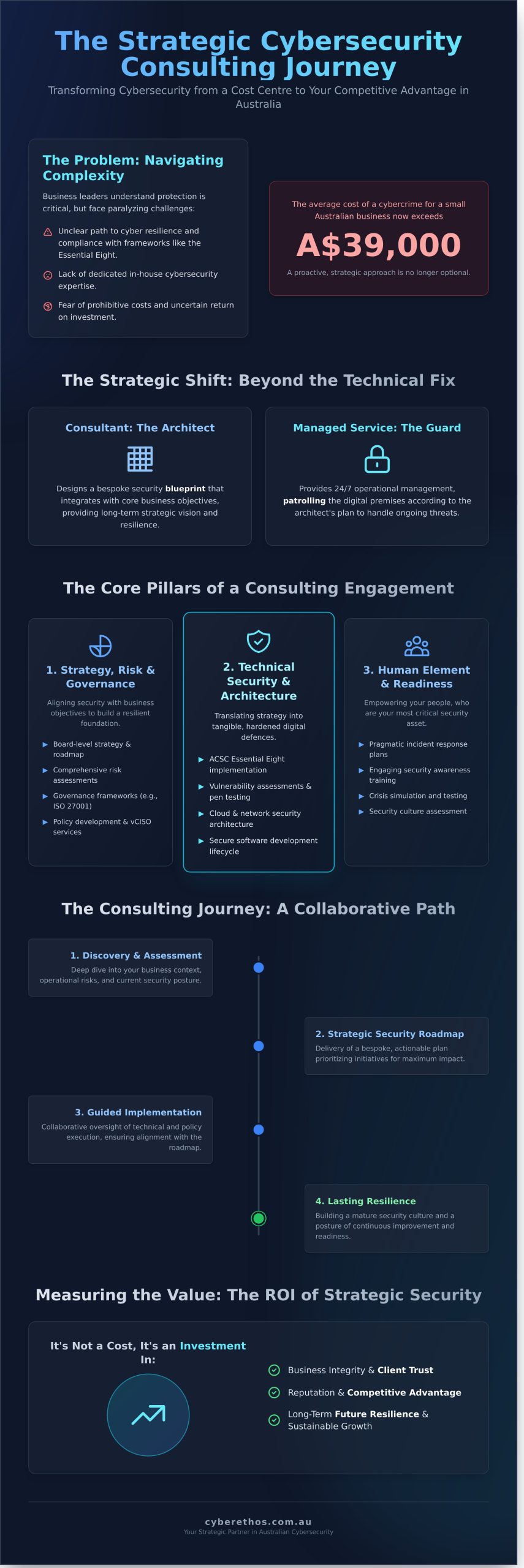
In today’s complex digital landscape, navigating Australian cybersecurity requirements can feel like a significant challenge. For many business leaders, the path to robust cyber resilience is unclear. You understand that protection is critical, but the complexities of frameworks like the Essential Eight, a lack of dedicated in-house expertise, or the fear of prohibitive costs can be paralyzing. This is where strategic cybersecurity consulting transforms from a daunting necessity into your greatest competitive advantage.
This guide is designed to provide clarity and direction. We will demystify the consulting process, showing you exactly how to choose the right partner to build lasting resilience and secure your business’s future. You will gain an actionable framework for turning cybersecurity from a cost centre into a strategic enabler, giving you the confidence that your organisation is not just protected and compliant, but primed for sustainable growth.
Key Takeaways
- View cybersecurity consulting as a strategic partnership that aligns your security posture with core business objectives for sustainable growth.
- Discover the key criteria for choosing the right consultant in Australia, ensuring they understand both global threats and the local regulatory landscape.
- Gain a clear understanding of the collaborative consulting journey, from the initial assessment to the delivery of a bespoke, actionable security roadmap.
- Learn to articulate the ROI of security not as a cost, but as a crucial investment in your business’s integrity, reputation, and future resilience.
What is Cybersecurity Consulting? Beyond the Technical Fix
Many business leaders view cybersecurity as a purely technical problem—a digital lock to be installed and forgotten. True cybersecurity consulting, however, is a strategic partnership. It transcends the reactive ‘fix-it’ mentality to align your security architecture with your core business objectives, fostering sustainable growth and resilience. The goal is not just to plug holes, but to build a robust security posture that enables your business to operate with confidence.
This strategic approach involves a deep understanding of how foundational concepts in cybersecurity apply to your unique operational context. It differs fundamentally from a managed service. Think of it this way: a consultant is the architect, designing a bespoke security blueprint that integrates seamlessly with your business. A managed service, while crucial, is the 24/7 security guard who patrols the premises according to that plan. One provides the strategic vision; the other provides ongoing operational management.
Why Your Business Can’t Afford to Ignore It
With the average cost of a cybercrime for a small Australian business now exceeding A$39,000, a proactive strategy is no longer optional. Navigating the complex local regulatory landscape, including the Essential Eight framework and the SOCI Act, requires expert guidance. Demonstrating this due diligence doesn’t just mitigate risk—it builds profound trust with clients and partners, creating a distinct competitive advantage in a market that values integrity.
Common Problems a Consultant Solves
A strategic consultant brings clarity to complexity, providing clear, business-focused answers to the critical questions that challenge leadership teams. We help organisations move from uncertainty to a position of strength when they face issues like:
- Risk Identification: “I don’t know what my biggest digital risks are or where to start.”
- Compliance Navigation: “We need to meet our compliance obligations but don’t know how.”
- Board-Level Reporting: “Our board needs a clear, quantifiable picture of our cyber risk posture.”
- Incident Response: “We’ve had a security incident and need expert help to recover and rebuild.”
The Core Pillars of a Cybersecurity Consulting Engagement
Effective cybersecurity consulting moves beyond a simple checklist of technical fixes. It delivers a holistic strategy built on three interconnected pillars that together create genuine cyber resilience. This framework helps business leaders understand that security is not a single project, but an integrated function spanning strategy, technology, and people.
A truly valuable engagement addresses aspects of all three pillars. The right mix is always bespoke, tailored to your organisation’s specific goals, operational risks, and current security maturity. This ensures that investment is directed where it will have the greatest impact on protecting your business and enabling its growth.
Pillar 1: Strategy, Risk, and Governance
This foundational pillar aligns your security posture with your core business objectives. It involves developing a clear, board-level cybersecurity strategy and a practical roadmap for achieving it. We conduct comprehensive risk assessments to identify and prioritise threats unique to your Australian operations, building robust governance frameworks (such as those aligned with ISO 27001) and clear policies. Foundational resources, like the Australian government’s cyber security checklist, provide a practical starting point for this process, which we then elevate with strategic leadership, often through services like our CISO as a Service (vCISO).
Pillar 2: Technical Security and Architecture
Here, strategy is translated into tangible defences. This pillar focuses on the integrity of your digital infrastructure, from on-premise networks to complex cloud environments. Our consultants guide the implementation of critical technical controls, including the Australian Cyber Security Centre’s Essential Eight, to create a hardened defensive posture. This work includes overseeing technical vulnerability assessments, penetration testing, and advising on the security of your software development lifecycle and critical supply chain dependencies.
Pillar 3: The Human Element and Incident Readiness
Technology and policy are only effective when supported by your people. This pillar addresses the human element of security, which is often the most critical. It involves developing and testing pragmatic incident response plans so your team knows exactly what to do in a crisis. We focus on empowering your staff through engaging cybersecurity awareness training and work to assess and strengthen your organisation’s overall security culture. This proactive preparation builds resilience and ensures a swift, coordinated response when it matters most.
The Consulting Journey: What to Expect from Your Partner
Engaging in cybersecurity consulting is not a transaction; it’s the beginning of a strategic partnership. This journey is built on a foundation of collaboration and transparency, designed to move your organisation toward a state of lasting cyber resilience. By understanding the process from the first conversation to the final strategic roadmap, you can enter this partnership with confidence, knowing exactly what to expect as we work to secure your business’s future.
Phase 1: Discovery and Strategic Alignment
Our engagement begins with a deep-dive consultation to understand your unique business landscape. We focus on your commercial goals, operational challenges, and specific pain points. This initial phase is dedicated to defining a clear scope, establishing key objectives, and agreeing upon the metrics that will define success. It’s about ensuring a perfect strategic fit, aligning our expertise with your vision before any technical work commences.
Phase 2: Assessment and Analysis
With a shared understanding in place, our consultants conduct a comprehensive analysis of your current security posture. This involves a blend of stakeholder interviews, policy and documentation reviews, and non-intrusive technical scans. The goal is to build a 360-degree view of your environment, identifying critical gaps, vulnerabilities, and areas of non-compliance against frameworks like the Essential Eight. You will receive an initial findings report, providing a clear and transparent snapshot of your current state.
Phase 3: Strategy, Recommendations, and Roadmapping
This is where analysis transforms into action. We translate our findings into a prioritised, actionable strategic roadmap designed for long-term resilience. This plan moves beyond a simple checklist, aligning with best practices outlined in Gartner’s guide to cybersecurity strategy to ensure your security investment drives tangible business value. The roadmap is presented to leadership in clear business terms, complete with timelines, resource estimates, and expected outcomes, empowering you to make informed decisions.
Ready to build a more resilient future for your business? Start your journey with a complimentary discovery call.
How to Choose the Right Cybersecurity Consultant in Australia
Selecting the right partner is one of the most critical decisions you will make in strengthening your organisation’s cyber resilience. The goal is not to hire a technical vendor, but to engage a strategic advisor who understands your business objectives. The right cybersecurity consulting firm becomes an extension of your team, enabling growth by building a secure and trusted foundation.
To make an informed choice, evaluate potential partners against this practical checklist:
Evaluate Their Approach: Strategic Partner vs. Technical Vendor
A true partner focuses on your long-term success. They should translate complex technical risks into clear business impacts, speaking your language, not just jargon. Look for a practitioner-led team with real-world experience in building resilient organisations. Their primary goal should be to empower and upskill your internal team, fostering independence rather than creating a cycle of dependency on their services.
Verify Their Expertise and Local Knowledge
The Australian regulatory and threat landscape is unique. Your consultant must have deep, demonstrated expertise in local frameworks. Use these questions to verify their credentials:
- Regulatory Fluency: Do they have extensive experience implementing the Australian Signals Directorate’s Essential Eight framework and advising on compliance with the SOCI Act?
- Industry Certifications: Are their consultants certified with globally recognised credentials like CISSP, CISM, or CISA?
- Proven Track Record: Can they provide relevant case studies or references from Australian businesses of a similar size and industry to yours?
Assess Their Fit for Your Organisation (SME & NFP)
Effective security is not one-size-fits-all. For small-to-medium enterprises and not-for-profits, it’s crucial to find a consultant who can deliver scalable, pragmatic solutions that align with your budget and operational reality. A good consultant makes security feel accessible, not intimidating. They should prioritise integrity and a human-first approach, understanding that your people are your greatest asset and your first line of defence.
Measuring the Value: The ROI of Cybersecurity Consulting
For many Australian business leaders, the critical question is not if cybersecurity is important, but whether a consulting engagement is worth the cost. The most effective way to answer this is to shift the perspective: proactive cybersecurity is not an expense, but a strategic investment in your organisation’s resilience, integrity, and future growth. The return on this investment is measured not just in prevented losses, but in newly created opportunities.
A professional cybersecurity consulting engagement delivers value that is both tangible and measurable, providing a clear justification for the investment. The metrics of success extend far beyond technical controls, directly impacting your bottom line and competitive standing.
Reduced Risk and Cost Avoidance
The most immediate return is in mitigating financial and operational risk. By partnering with an expert consultant, you are actively avoiding costs that could cripple your business. Key areas of cost avoidance include:
- Data Breach Mitigation: The average cost of a data breach in Australia has reached A$4.03 million. A strategic security framework dramatically lowers the likelihood and potential impact of such an incident.
- Lower Insurance Premiums: A demonstrably strong security posture, often validated through audits and alignment with frameworks like the Essential Eight, can lead to significantly lower cyber insurance premiums.
- Regulatory Compliance: Avoiding substantial fines under Australian legislation, such as the Privacy Act’s Notifiable Data Breaches (NDB) scheme, is a direct financial benefit of a well-managed compliance program.
- Operational Continuity: Minimising downtime is critical. Every hour of disruption means lost revenue, decreased productivity, and potential damage to client relationships.
Business Enablement and Growth
Beyond defence, strategic security is a powerful business enabler. A mature cyber resilience program, guided by expert consulting, becomes a competitive advantage that fuels growth. It allows you to build a reputation for integrity and reliability, which is invaluable in today’s digital economy. A strong security posture enhances customer trust, streamlines internal processes for greater efficiency, and unlocks new revenue streams by helping you meet the stringent security requirements for high-value government and enterprise contracts.
Ultimately, investing in your security framework is investing in your brand’s future. It demonstrates a commitment to operational excellence and the protection of your clients, partners, and people. Invest in your resilience. Talk to a Cyber Ethos strategist today.
Your Strategic Partner in Cyber Resilience
Navigating Australia’s complex digital landscape requires more than just technical fixes; it demands a strategic vision and a trusted partner. As we’ve explored, the right engagement moves beyond reactive measures to build genuine, long-term cyber resilience, transforming your security posture from a necessary expense into a proactive asset. Effective cybersecurity consulting is the key to unlocking this strategic advantage, enabling growth while protecting your organisation’s integrity and reputation.
At CyberEthos, our practitioner-led team embodies this partnership philosophy. With extensive Australian industry experience, we guide Small and Medium-sized Enterprises (SMEs) and Not-for-Profits (NFPs) through the specific demands of the local landscape, including mastery of the Essential 8 framework and compliance with the SOCI Act. We are committed to building trusted, long-term partnerships that empower your business to operate with confidence and clarity.
Take the decisive step from vulnerability to resilience. Schedule a no-obligation consultation to map your path to cyber resilience.
Frequently Asked Questions
What’s the difference between cybersecurity consulting and a CISO as a Service?
Cybersecurity consulting is typically project-based, focused on achieving a specific outcome within a defined timeframe—such as a risk assessment or an Essential Eight audit. In contrast, a CISO as a Service (vCISO) provides ongoing, embedded strategic leadership. The vCISO acts as a part of your executive team to guide your long-term security program, manage risk, and foster a culture of cyber resilience, offering continuous governance rather than a one-time solution.
How much does cybersecurity consulting cost for an SME in Australia?
For an Australian SME, costs are bespoke to your unique requirements. A foundational project, like a comprehensive security risk assessment or a policy framework development, can range from A$8,000 to A$25,000. This investment delivers a strategic roadmap for security maturity. More complex engagements are quoted based on scope, always ensuring the investment aligns with tangible risk reduction and supports your business objectives, providing a clear return on security investment.
How long does a typical consulting engagement take?
The duration of an engagement is directly tied to its strategic goals. A targeted assessment, such as a gap analysis against the Essential Eight framework, might take two to four weeks. A more comprehensive project, like preparing for ISO 27001 certification or developing a full cyber resilience strategy, could span several months. We establish clear timelines from the outset, ensuring milestones are met with minimal disruption to your core operations.
Our business is small. Do we really need a cybersecurity consultant?
Absolutely. Cyber threats do not discriminate by size; in fact, SMEs are often targeted due to perceived weaker defences. A consultant provides the strategic expertise to build a strong yet proportionate security foundation, protecting your critical data and client trust. This is not just a defensive measure but a proactive investment in your business’s integrity and reputation, enabling you to grow safely and confidently in a complex digital environment.
What happens after the consulting project is finished?
A successful project concludes with a clear path forward. We provide a detailed report, a strategic roadmap with prioritised actions, and the knowledge your team needs to maintain its improved security posture. Our goal is to empower your organisation for long-term resilience. Many clients choose to retain our services for ongoing advisory or vCISO support to ensure their security strategy evolves in step with new threats and business growth.
Can a consultant help us respond to an active cyber attack?
Yes, specialist consultants offer critical incident response (IR) services. If you are facing an active attack, an IR consultant can help contain the threat, eradicate the adversary from your network, and guide you through recovery. Their role is to minimise damage, preserve evidence for investigation, and restore business operations securely and efficiently. This immediate, expert intervention is vital for navigating the technical and reputational complexities of a security breach.

