Booking.com Breach Exposes a Hidden Gap in Board Oversight Now
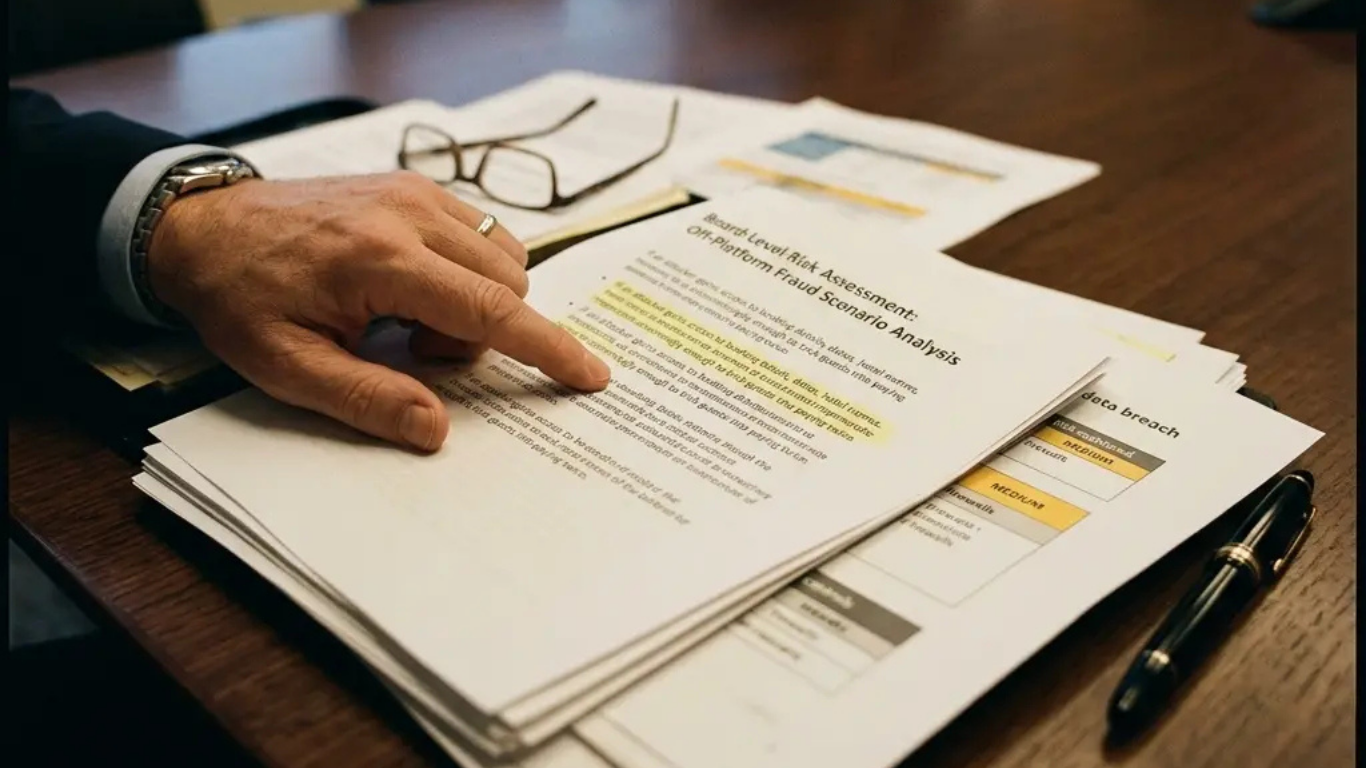
The Booking.com breach has done more than expose millions of travelers’ data — it has exposed something far more uncomfortable: the gaps that boards are still not governing. Here’s what that looks like in the Booking.com context. The Booking.com Breach and the Risk Document That Doesn’t Exist After a breach like this, someone will eventually … Read more